38 aws security best practices
docs.aws.amazon.com › IAM › latestSecurity best practices in IAM - AWS Identity and Access ... Jul 14, 2022 · Use the root user to complete the tasks that only the root user can perform. For the complete list of these tasks, see Tasks that require root user credentials in the AWS General Reference. For more information, see Best practices to protect your account's root user in the AWS Account Management User Guide. docs.aws.amazon.com › whitepapers › latestAWS Security Best Practices - AWS Security Best Practices AWS Security Best Practices. Notice: This whitepaper has been archived. For the latest technical information on Security and Compliance, ...
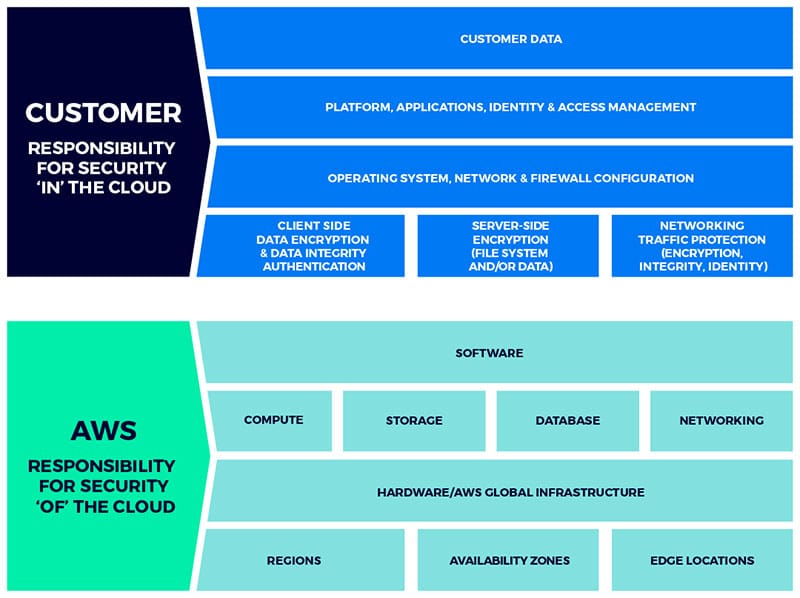
d1.awsstatic.com › AWS_Security_Best_PracticesAWS Security Best Practices Amazon Web Services AWS Security Best Practices Page 1 Introduction Information security is of paramount importance to Amazon Web Services (AWS) customers. Security is a core functional requirement that protects mission- critical information from accidental or deliberate theft, leakage, integrity compromise, and deletion.
Aws security best practices
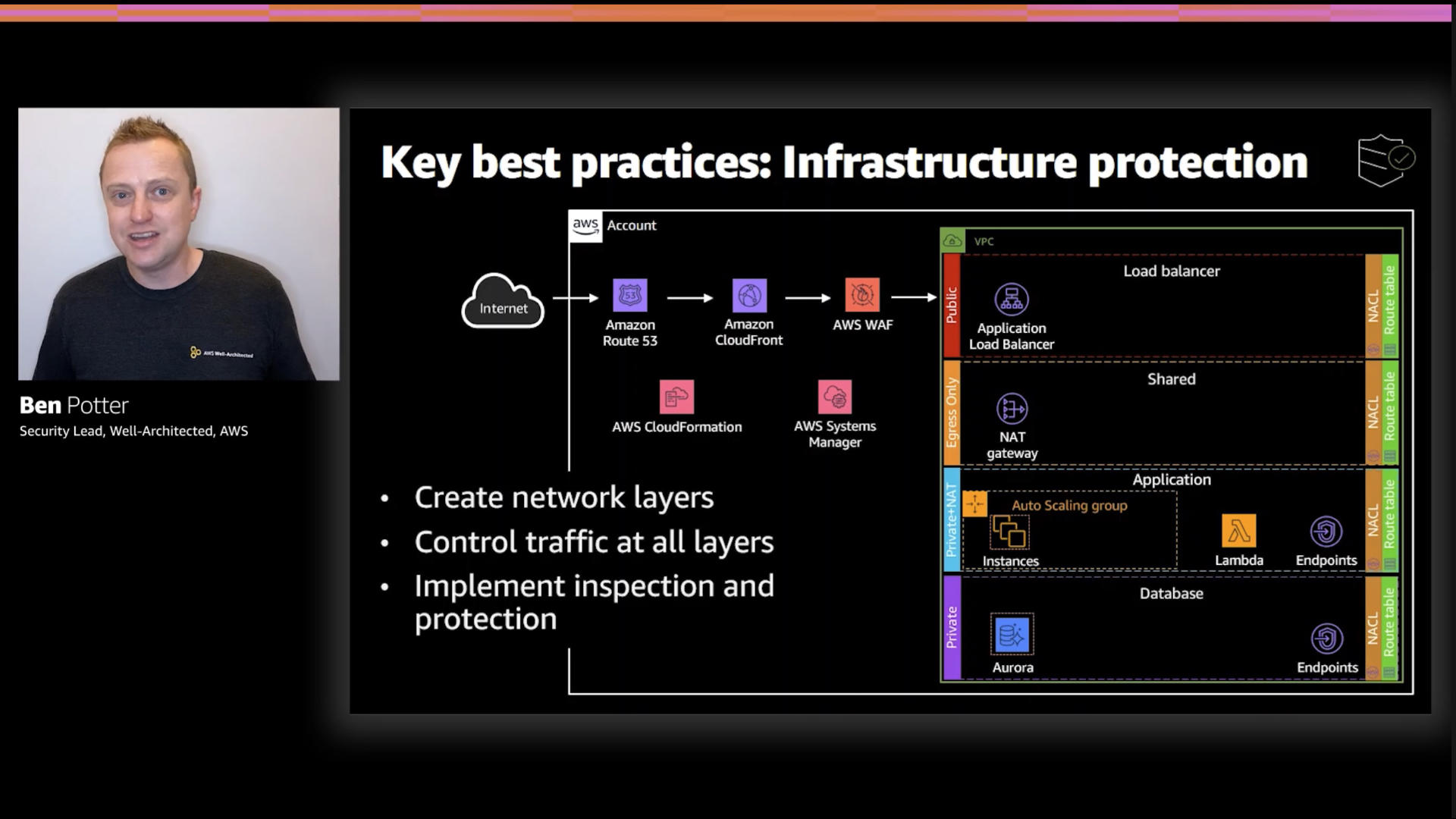
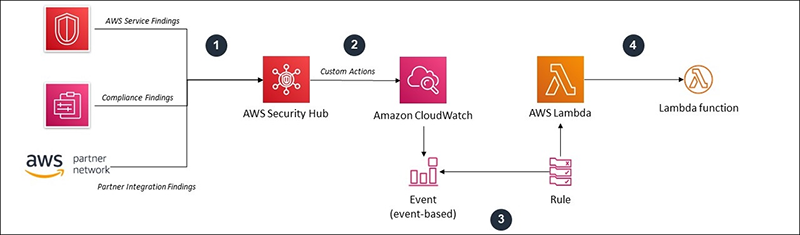
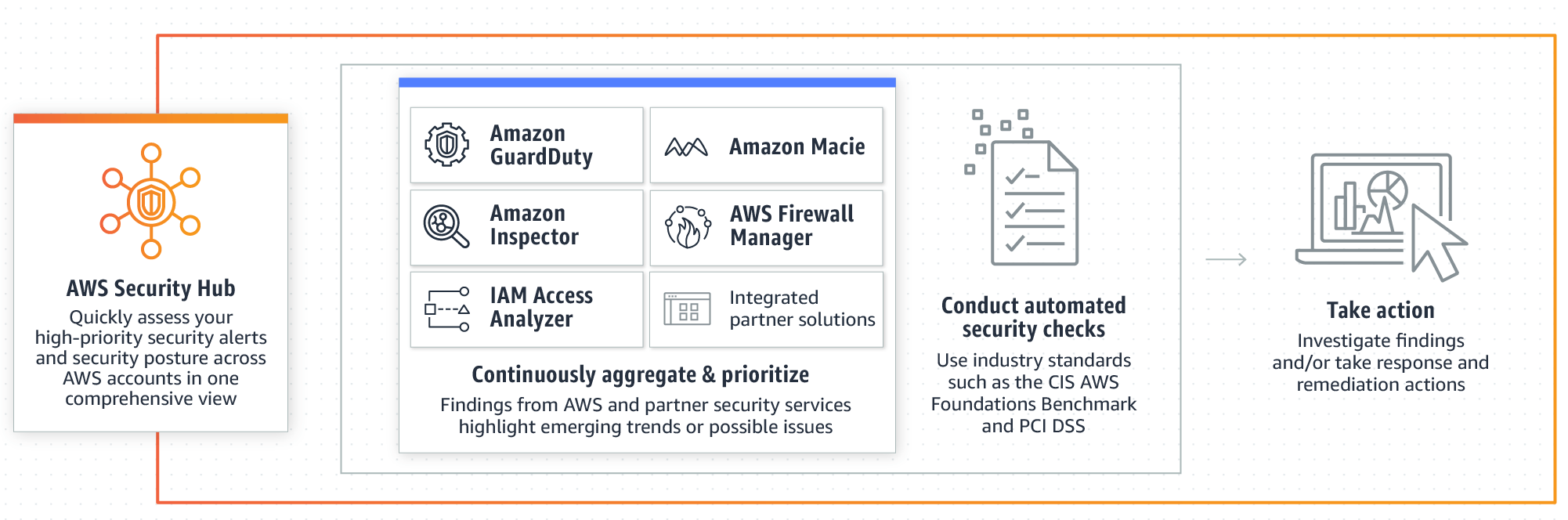
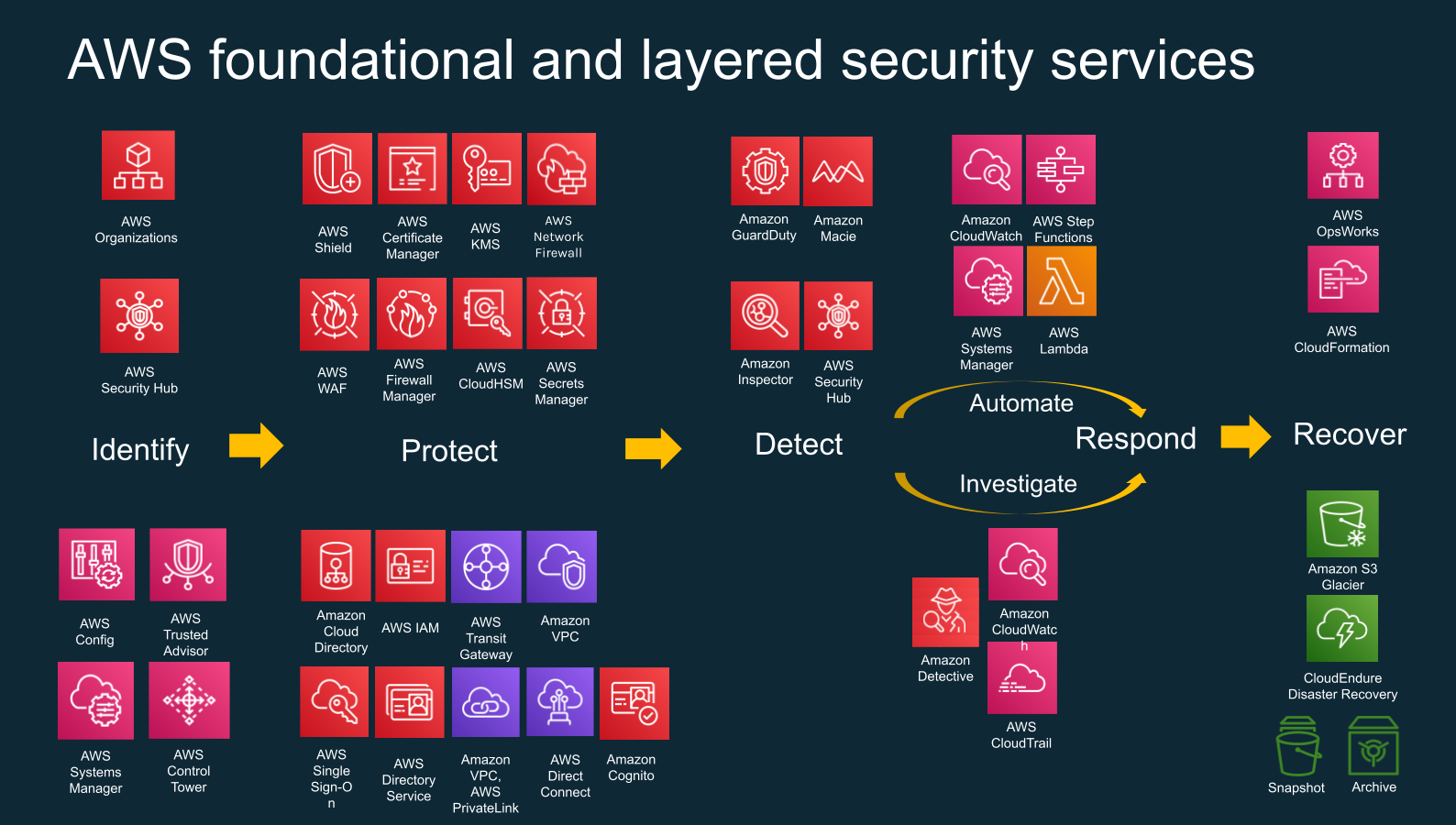
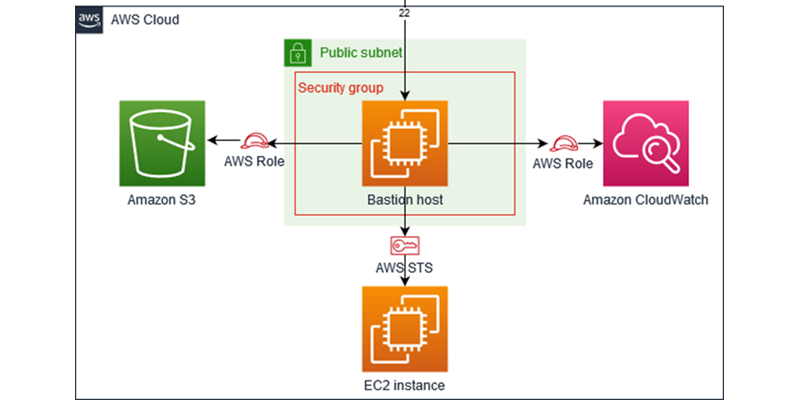
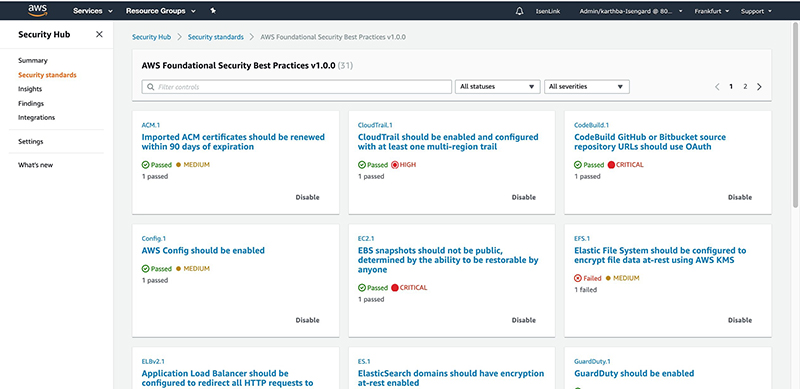
docs.aws.amazon.com › securityhub › latestAWS Foundational Security Best Practices controls - AWS ... For change triggered controls, you must record resources in AWS Config for the control to work. For more information, see AWS Config resources required for AWS Foundational Security Best Practices controls. The required AWS Config rule, and any specific parameter values set by AWS Security Hub. Remediation steps aws.amazon.com › architecture › security-identitySecurity, Identity & Compliance | AWS Architecture Center Best Practices for Security, Identity, & Compliance Learn how to meet your security and compliance goals using AWS infrastructure and services. To learn current AWS recommendations and strategies to use when designing cloud architectures with security in mind, see the Security Pillar - AWS Well-Architected Framework . aws.amazon.com › blogs › securitySecurity practices in AWS multi-tenant SaaS environments Jan 31, 2022 · While security is a foundational element of any software application, specific considerations apply to SaaS applications. This post dives into the challenges, opportunities and best practices for securing multi-tenant SaaS environments on Amazon Web Services (AWS). SaaS application security considerations
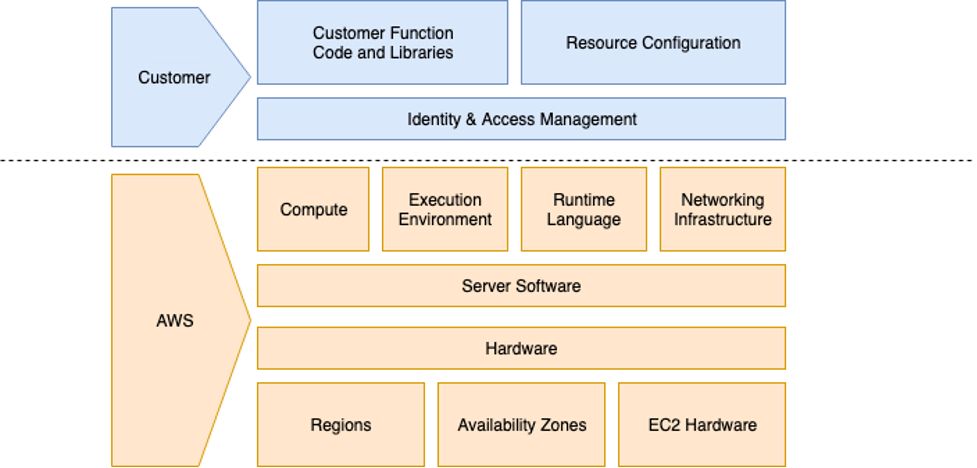
Aws security best practices. docs.aws.amazon.com › lambda › latestBest practices for working with AWS Lambda functions The AWS Lambda execution environment contains a number of libraries such as the AWS SDK for the Node.js and Python runtimes (a full list can be found here: Lambda runtimes). To enable the latest set of features and security updates, Lambda will periodically update these libraries. aws.amazon.com › blogs › securitySecurity practices in AWS multi-tenant SaaS environments Jan 31, 2022 · While security is a foundational element of any software application, specific considerations apply to SaaS applications. This post dives into the challenges, opportunities and best practices for securing multi-tenant SaaS environments on Amazon Web Services (AWS). SaaS application security considerations aws.amazon.com › architecture › security-identitySecurity, Identity & Compliance | AWS Architecture Center Best Practices for Security, Identity, & Compliance Learn how to meet your security and compliance goals using AWS infrastructure and services. To learn current AWS recommendations and strategies to use when designing cloud architectures with security in mind, see the Security Pillar - AWS Well-Architected Framework . docs.aws.amazon.com › securityhub › latestAWS Foundational Security Best Practices controls - AWS ... For change triggered controls, you must record resources in AWS Config for the control to work. For more information, see AWS Config resources required for AWS Foundational Security Best Practices controls. The required AWS Config rule, and any specific parameter values set by AWS Security Hub. Remediation steps

























0 Response to "38 aws security best practices"
Post a Comment